CURRENT AFFAIRS
Get the most updated and recent current affair content on Padhaikaro.com
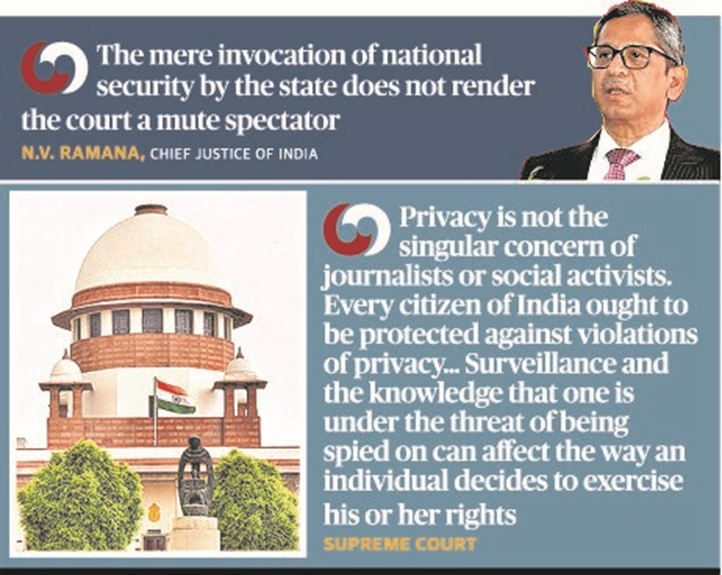
Pegasus snooping case
- IAS NEXT, Lucknow
- 20, Dec 2021

The Supreme Court has stayed further proceedings of a Commission of Inquiry appointed by the West Bengal Government to look into allegations of snooping using the Pegasus software.
What’s the issue?
The continued use of spyware Pegasus, which an Israeli company sells to governments worldwide, has been confirmed with fresh reports. Like the phones it targets, Pegasus has been apparently updated and now comes with new surveillance capabilities.
What is Pegasus?
It is a spyware tool developed by an Israeli firm, the NSO Group.
Spyware spy on people through their phones.
- Pegasus works by sending an exploit link, and if the target user clicks on the link, the malware or the code that allows the surveillance is installed on the user’s phone.
- Once Pegasus is installed, the attacker has complete access to the target user’s phone.
What can Pegasus do?
- Pegasus can “send back the target’s private data, including passwords, contact lists, calendar events, text messages, and live voice calls from popular mobile messaging apps”.
- The target’s phone camera and microphone can be turned on to capture all activity in the phone’s vicinity, expanding the scope of the surveillance.
What is a zero-click attack?
A zero-click attack helps spyware like Pegasus gain control over a device without human interaction or human error.
- So all awareness about how to avoid a phishing attack or which links not to click are pointless if the target is the system itself.
- Most of these attacks exploit software which receive data even before it can determine whether what is coming in is trustworthy or not, like an email client.
What’s the Difference Between Malware, Trojan, Virus, and Worm?
Malware is defined as a software designed to perform an unwanted illegal act via the computer network. It could be also defined as software with malicious intent.
Malware can be classified based on how they get executed, how they spread, and/or what they do. Some of them are discussed below.
- Virus: A program that can infect other programs by modifying them to include a possible evolved copy of itself.
- Worms: Disseminated through computer networks, unlike viruses, computer worms are malicious programs that copy themselves from system to system, rather than infiltrating legitimate files.
- Trojans: Trojan or trojan horse is a program that generally impairs the security of a system. Trojans are used to create back-doors (a program that allows outside access into a secure network) on computers belonging to a secure network so that a hacker can have access to the secure network.
- Hoax: An e-mail that warns the user of a certain system that is harming the computer. The message thereafter instructs the user to run a procedure (most often in the form of a download) to correct the harming system. When this program is run, it invades the system and deletes an important file.
- Spyware: Invades a computer and, as its name implies, monitors a user’s activities without consent. Spywares are usually forwarded through unsuspecting e-mails with bonafide e-mail i.ds. Spyware continues to infect millions of computers globally.